XKCD #936: Password Strength
Original date: 2021-02-17.
Last updated: 2021-03-05.
Here's something interesting I noticed: 36^15 is exactly equal to (6^5)^6. Why is this relevant?
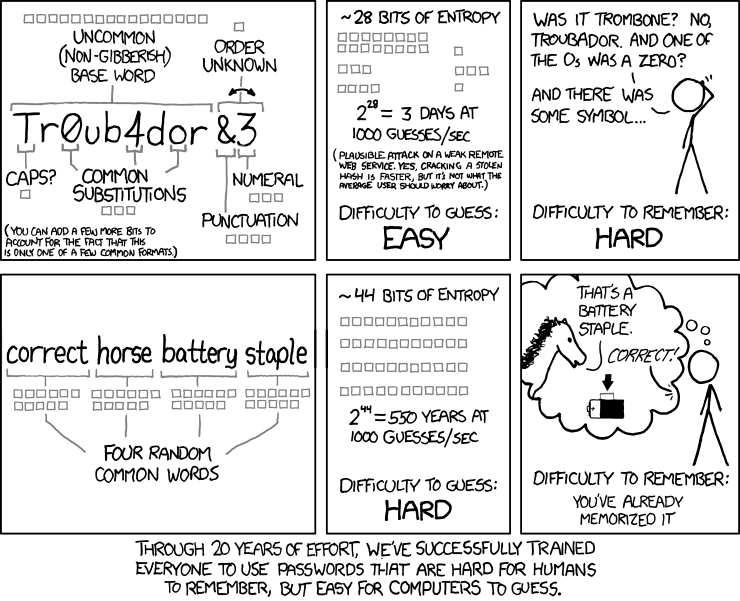
A popular passphrase generation method is Diceware: you concatenate words from a list chosen by rolling physical dice. Such a passphrase is stronger and easier to remember than the alternatives:
This is reasonable for the average user's password manager. With the EFF's short word list and four rolls of 4d6, they'll get four easy words to remember and 41 bits of entropy which is plenty of security for their threat model.
This may not be enough for us tech nerds though, for our password managers securing our cloud computing accounts. Security professionals now recommend using 6 words from a 5-die word list, giving you 77.5 bits of entropy.
Unfortunately this also takes a while to type. The EFF's five-die word list averages 7 characters per word so you're looking at about 42 characters or 47 with a delimiter.
My web browser doesn't store cookies so I log in to my password manager pretty often. Diceware is too long for comfort. Can we do better without compromising security?
I've never found it hard to memorize stuff so I always preferred just using random characters. This hasn't been comfortable to type either though because you need to press shift so much for uppercase characters and symbols. So I decided to just leave them out.
There are 26 lowercase letters and 10 numbers, so 36 total. How many such characters do you need to get the same entropy as Diceware?
As it turns out, the funny mathematical equivalence above means 15 lowercase letters or numbers gives you the exact same entropy as a 6-word 5-die passphrase: 77.5 bits. It's about 1/3 the characters, still no shift key and no spaces. Same security, a bit harder to remember, but way easier to type. Type it a couple times a day and you'll soon be able to bang out your passphrase instantly.
(More precisely: if you type 100 words per minute, that's roughly 8 characters per second; with practice you'll be able to comfortably type it in well under two seconds.)
Compare passwords generated in these styles:
Lowercase alphanumeric:
Diceware:
(Spaces added for readability)
The security characteristics of these passwords are identical. Which of these would you rather memorize? Which one would you rather type in every day?
If like me you used to memorize digits of pi for fun, if you accidentally memorized your Diablo II CD keys decades ago and still remember them, if you're planning on typing this in several times a day, you're not going to have trouble memorizing random characters. Just use a lowercase alphanumeric passphrase and enjoy typing it in.
I'm told by friends that the above might be a little crazy even for IT professionals. So here's a potential compromise.
The EFF publishes a special 4-die word list where every 3-letter prefix is unique. This means you can memorize a set of words, but use only the first three letters of each word as your password.
(The article that introduces these lists suggests this could be used with special software for autocomplete or error correction. I'm not sure why they didn't suggest this much simpler use for it.)
Since there aren't as many words you need more of them for similar security. You'll need seven words for 72.4 bits or eight words for 82.7 bits. (This exactly matches the entropy of 14 or 16 random lowercase letters or numbers since (6^4)^n == 36^(2n).)
Here's a seven word generator:
Words:
Password:
(Spaces added for readability)
This is a 21 character password, half the number of characters of the full 6-word 5-die Diceware. It's an extra word to remember but the word list is shorter so the words may not be as esoteric. A bit worse security, similar memorization difficulty, but half the typing!
I guess what I'm trying to say is, you don't have to take Diceware at face value, and you don't have to give up on security either. You can modify it for usability or ignore it entirely without compromising security. Do what is best for you.